Ethical hacking is the topic of this introduction letter to our seminar on Ethical Hacking: Its Role in the Modern Age Cyber Security. It doesn't matter if you're a beginner wanting to learn better or someone wishing to improve on his knowledge of cybersecurity; this seminar is all about making the person know essential things about ethical hacking and its importance in protecting organizations against cyber threats.
Overview of Ethical Hacking
The seminar will introduce ethical hacking to participants. Hence, it will be clear for participants what an ethical hacker would do. You will learn why ethical hacking is emphasized in the cyberspace physical world, and ethical hackers' roles would be revealed with respect to how they can protect organizations from attacks.
- Difference between Ethical and Malicious Hacking:
We will describe the key differences between both types of hackers, Ethical or White Hats and Malicious or Black Hats, based on the roles, objectives, and methods. This is also a basis of how ethical hacking fits in within the entire field of cybersecurity.
- Types of Hackers:
These would include the various types of hackers to which the participants are exposed:
White Hat Hackers - Ethical hackers who utilize skills to improve security Black Hat Hackers - Malicious hackers who exploit vulnerabilities for harmful purposes Gray Hat Hackers - Those who fall into the middle ground sometimes doing not strictly unethical activities, but do not actually harm anyone either.
Five Phases of Ethical Hacking
The following five phases of hacking: inform how ethically a vulnerability is discovered, the security is pried into, and how tests cannot come through defenses.
Reconnaissance: At this stage, the ethical hacker captures all critical information of the target system. Also, participants will learn how ethical hackers perform reconnaissance to identify potential entry points without causing harm.
Scanning: Ethical hackers scan the target system at this phase for discovering possible weaknesses that the malicious hackers could exploit.
Gaining Access: After identifying some weaknesses, ethical hackers try to access the system, mimicking what an attacker would most likely do to gain entry. This phase thus enables organizations to detect and remedy security breaches.
Maintaining Access: These techniques are used to determine how long an attacker can maintain access once inside. Ethically hacking organizations are generalized in preventing long-term violations.
Covering Tracks: "Ethical hackers attempt to cover their tracks just to check the efficacy of a security system on detecting and defending against malicious activity. Thus, participants will understand how covering of tracks helps in real-world security testing."
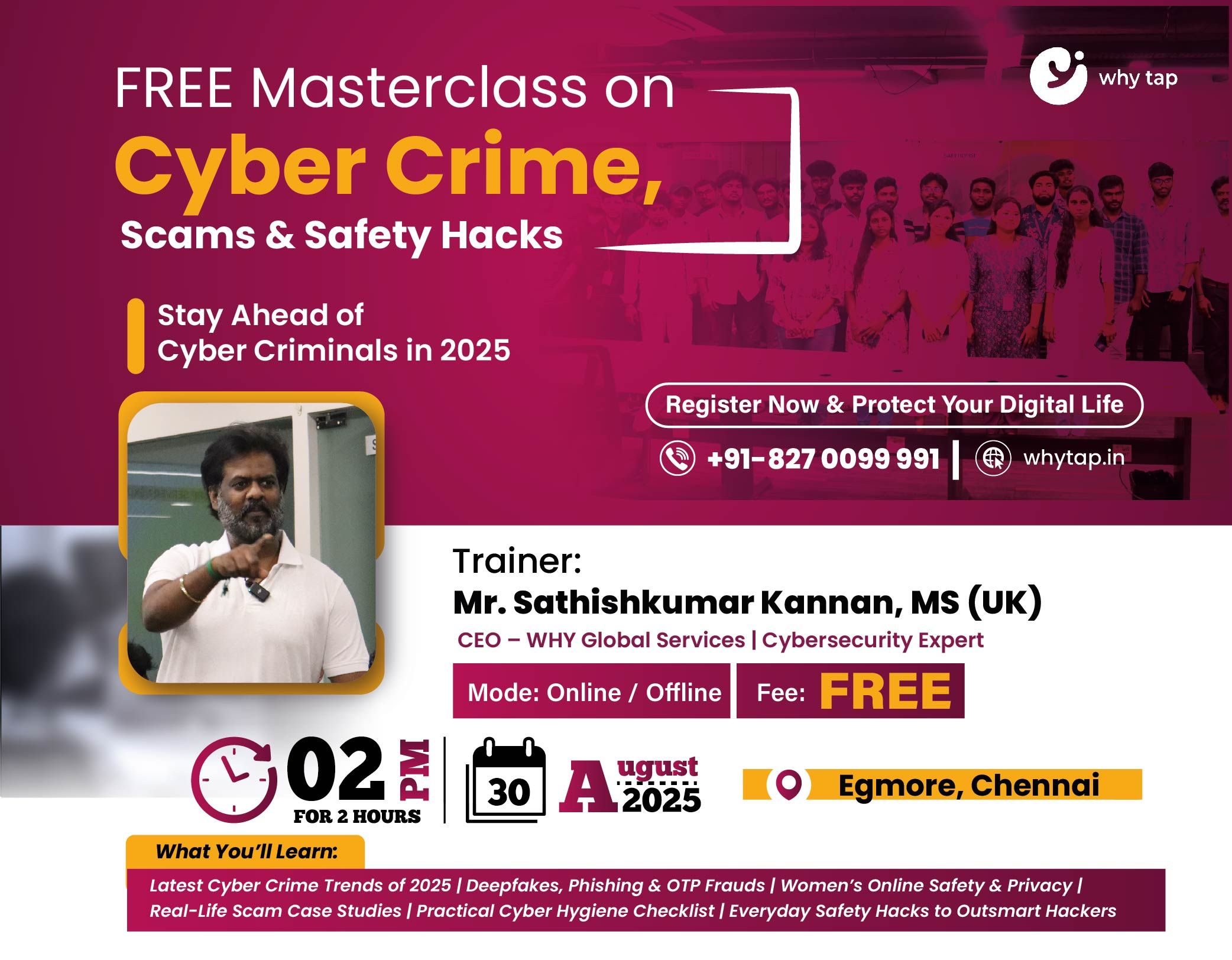
Why To Attend?
Hands-On Experienc: This will include giving an understanding of the practical things involving ethical hacking techniques through which one might protect organizations. Expert Guidance: Learn from some experienced ethical hacking professionals who have worked in real-world scenarios. Boost Your Cybersecurity Knowledge: Understand the principles and phases of ethical hacking that will help you to get into the field of cybersecurity: Interactive Sessions: Engage in Q&A sessions and discussions to clarify doubts and enhance your learning experience.
This opportunity will unveil for you how ethical hacking works and how to protect systems from malicious cyber threats. So register now before the opportunity closes!